Oliver Page
Email Threat Management
April 29, 2026
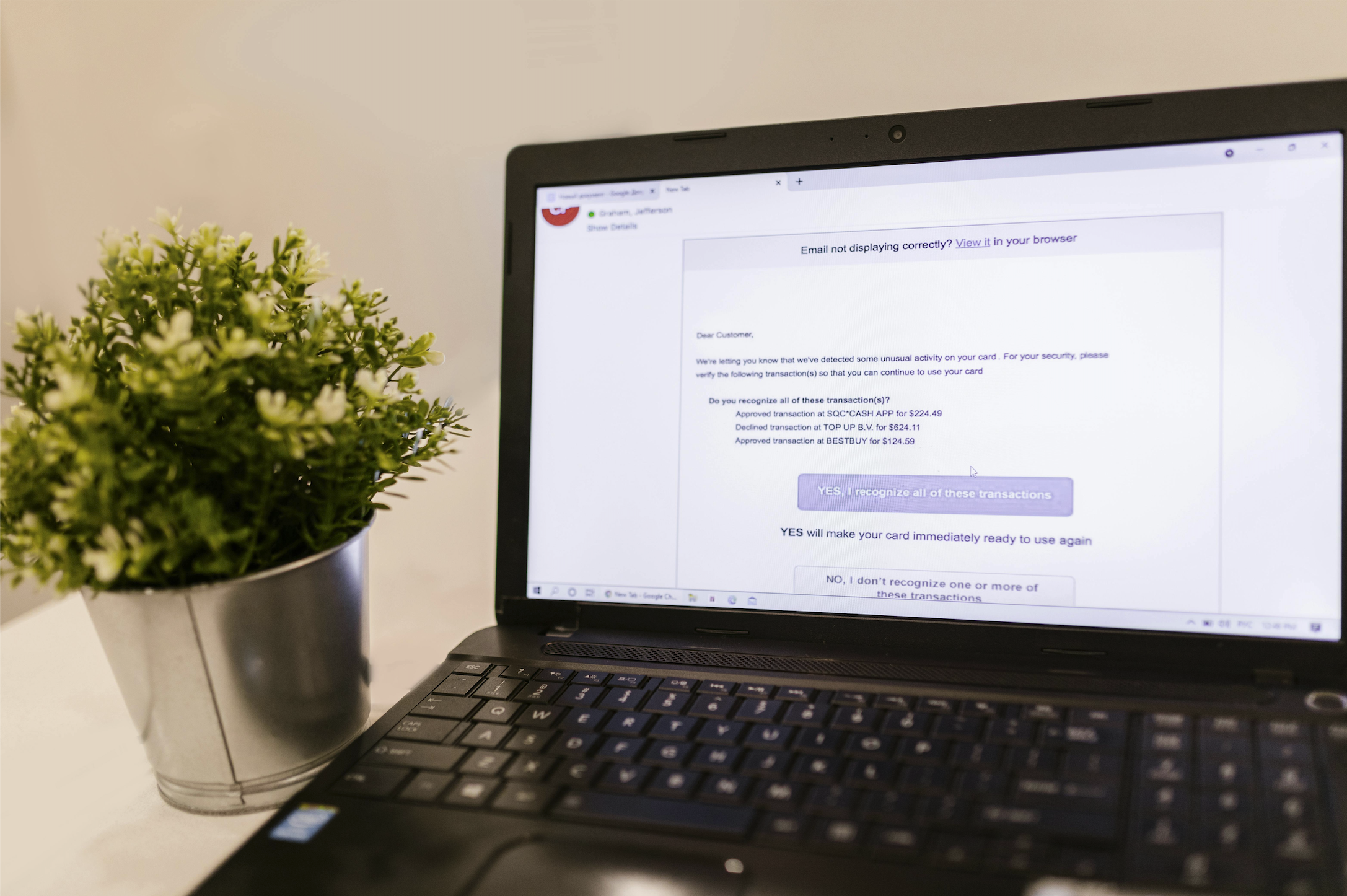
Phishing simulation training works. Across 400+ school districts using CyberNut, average click rates on simulated phishing emails drop by 75%. That is a meaningful, measurable reduction in risk. But “reduced” is not “eliminated.” The gap between those two words is where real breaches happen: a teacher clicks a credential-harvesting link on a Friday afternoon, and nobody catches it until Monday. For K-12 IT directors and CTOs, the strategic question is not whether to invest in training. It is what closes the gap that training, no matter how effective, will always leave behind. The answer is integrated threat triage and removal.
Phishing simulation training builds a foundational security layer for school districts: human awareness. When staff learn to recognize social engineering tactics, they stop clicking. They start reporting. They talk to colleagues about suspicious messages, which spreads vigilance organically across a building. CyberNut’s gamified 30-second micro-lessons vs. 30-minute videos drive dramatically higher completion rates than traditional training, which means awareness actually reaches the people who need it. Adaptive simulations reinforce that awareness by testing staff with realistic phishing scenarios tailored to K-12 contexts. For a deeper look at how simulations work, see this phishing simulation primer for school IT leaders. Training is the right starting point. The mistake is treating it as the finish line.
No. Training is necessary, but it is not sufficient. Even the strongest training program cannot eliminate human error entirely. Industry research consistently ranks phishing among the most common attack vectors targeting K-12 education, and the volume of phishing attempts reaching school districts continues to grow. A 75% reduction in click rates still leaves one in four previously susceptible staff members clicking. In a district with thousands of staff and students, that residual percentage translates to real, recurring exposure every time a phishing campaign reaches inboxes. Training changes behavior at scale; it does not change the fact that some percentage of people, on some percentage of days, will make a mistake. Threat triage and removal exist to address exactly that reality.
Consider a district with 2,000 staff members. Before training, assume a click rate that generates consistent exposure. After effective training reduces that rate by 75%, the district has made enormous progress. But the remaining 25% of the original risk does not disappear. It recurs with every new phishing email that lands in an inbox. Over the course of a school year, hundreds of phishing attempts may reach staff. Even with well-trained staff, the math produces a predictable number of clicks. Each click is a potential credential compromise, a ransomware entry point, or a FERPA data exposure. The residual risk is not theoretical. It is arithmetic. K-12 IT directors who have deployed training and seen their metrics improve are right to feel good about that progress, but the remaining gap demands a different kind of solution: one that triages reported and detected threats and removes them at the source, not just one that reduces the likelihood of interaction.
Phishing emails that go unclicked do not become harmless. They sit in inboxes, waiting. A staff member who correctly ignored a suspicious message on Tuesday morning may revisit that same inbox on Wednesday afternoon, tired and distracted, and click. Dwell time, the period a malicious email remains accessible, directly increases the probability of compromise. When someone does click, the damage can spread laterally: compromised credentials enable attackers to send internal phishing emails that bypass spam filters entirely. For a district IT team of one to five people, manually triaging staff reports, hunting through thousands of mailboxes, and deleting confirmed malicious emails is an enormous time burden. Without integrated triage and removal, those emails persist. Every hour they remain is another hour of exposure.
Enterprise cybersecurity frameworks assume the existence of a Security Operations Center: a dedicated team of analysts who monitor alerts, triage reported threats, and remediate incidents in real time. School districts do not operate this way. A typical district IT department has one to five staff members responsible for everything from projector bulbs to firewall configurations. There is no dedicated security analyst. There is no 24/7 monitoring team. As this comparison of K-12 vs. enterprise phishing simulation explains, the operational assumptions behind enterprise tools simply do not fit school district realities. K-12 needs a security model that accounts for small teams, tight budgets, and the absence of specialized security personnel. Bolting enterprise threat remediation onto a school district’s workflow creates more problems than it solves.
Genuine integration means training, simulation, staff reporting, threat triage, and removal operate within a single system and inform each other continuously. When a staff member reports a suspicious email, the platform triages it: analyzing the message, classifying the threat, and determining intent. If confirmed malicious, it removes every instance of that email from every inbox across the district in a single action. Simulation data identifies which staff members are most susceptible, so training adapts accordingly. Reporting patterns reveal which types of phishing emails bypass awareness, which informs future simulation design. CyberNut’s platform combines phishing simulation training with Advanced Threat Search, its email threat triage and removal tool, in one system. This is not three disconnected tools sharing a dashboard. It is a single feedback loop where each component strengthens the others.
The compounding effect is straightforward. Training shrinks the attack surface by reducing the number of staff members who will interact with a phishing email. Threat triage and removal contain what gets through by analyzing reported and detected emails, classifying their intent, and pulling the malicious ones out of inboxes before they can be clicked. Together, these functions multiply each other’s effectiveness. Training alone reduces risk by a fixed percentage. Triage and removal alone reduce dwell time. Combined, each click that training prevents is one less incident the platform needs to triage, and each email that the platform identifies and extracts is one less opportunity for a trained staff member to make a mistake on a bad day. Staff who are trained to report suspicious emails feed the triage and removal system, which protects the entire district. The cycle accelerates over time.
When evaluating vendors, K-12 IT directors should ask a specific question: does the platform’s training data directly inform its triage and removal actions, and vice versa? If simulation results live in one system while triage and removal operate in another, the integration is cosmetic. True integration means a staff member’s report of a suspicious email triggers automated triage and district-wide removal without requiring the IT team to log into a separate tool, export data, or manually correlate findings. Other evaluation considerations include FERPA compliance (mandatory for any tool handling student or staff data), speed of deployment for small IT teams, and whether the platform was built for K-12 from the ground up rather than repurposed from enterprise environments.
No. Training reduces the volume of threats that require triage and removal by making staff less likely to interact with phishing emails. Triage and removal handle the residual risk that training cannot eliminate. The two functions are complementary. Removing one weakens the other. Districts achieve the strongest protection when both operate together within a single platform.
Advanced Threat Search enables district IT staff to triage suspicious emails and remove malicious ones across every inbox in the district with a single action. This eliminates the need to manually search and clean mailboxes one by one, which is critical for teams of one to five people managing thousands of accounts.
Yes. CyberNut is FERPA-compliant, which means staff and student data is handled according to the privacy standards school districts are legally required to meet. Districts should verify FERPA compliance for any cybersecurity training or email management tool before deployment, as non-compliant tools can create the very data exposure risks they are meant to prevent.
Yes, if these functions are integrated into a single platform designed for small teams. CyberNut was built for K-12 from the ground up, meaning the interface, workflows, and automation are designed for IT departments without dedicated security analysts. The platform handles the complexity so the IT team does not have to.
CyberNut customers see phishing click rates drop by 75% on average. Because training, triage, and threat removal are deployed simultaneously from the same platform, districts begin reducing risk from both directions immediately rather than waiting to layer on a second tool months later.
The argument is not that training fails. Training succeeds. It transforms staff from passive targets into active participants in a district’s security posture. But training operates on probability; it makes clicks less likely. Triage and removal operate on certainty: triage classifies the threat, and removal makes malicious emails inaccessible across every inbox in the district. K-12 districts need both layers. The answer for school IT leaders is a system where staff are trained, simulations adapt, reporting is encouraged, and threats that slip through are triaged and removed before they spread. CyberNut delivers cybersecurity training plus threat triage and removal in a single platform trusted by 400+ school districts and used by over 400,000 staff and students.
Run Your Free Phishing Assessment. Takes 15 minutes. No commitment.
Oliver Page
Some more Insights


Back